








Some of the attendees
The Q & A session
Types of Data Security Threats
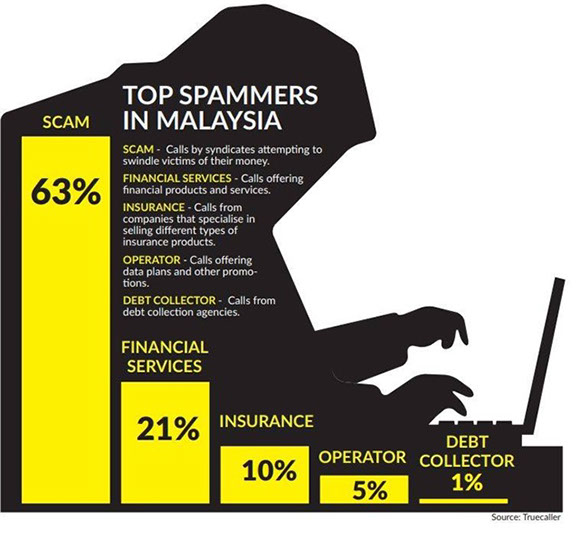
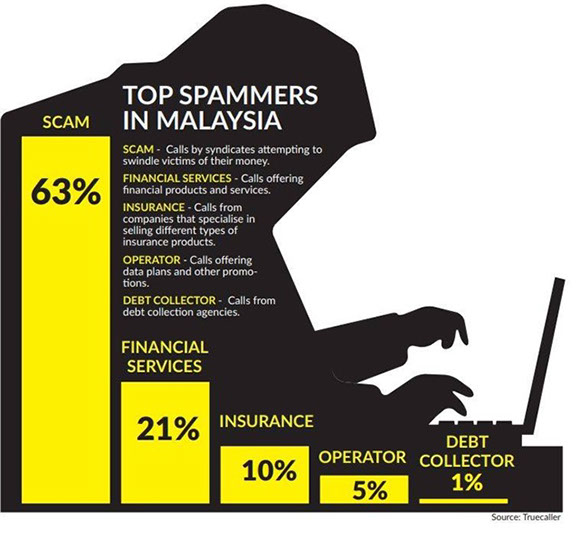
Types of Scammers in Malaysia
A token of appreciation delivered to the Speaker
first |<<
< prev
next >
>>| last
5 - 5
A vi









Some of the attendees
The Q & A session
Types of Data Security Threats
Types of Scammers in Malaysia
A token of appreciation delivered to the Speaker
first |<<
< prev
next >
>>| last
5 - 5
A vi